At a Glance
Discovery science and technical innovation
Computing at LLNL advances scientific discovery through foundational and innovative research; mission-driven data science; complex modeling, simulation, and analysis on powerful supercomputers; and creative technologies and software solutions. Everything at Livermore is Team Science. Thus, Computing is at the heart of many of LLNL’s most compelling national security and scientific efforts:
- Operating one of the world’s largest HPC data centers
- Designing AI and machine learning algorithms for science-based pattern discovery
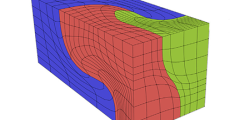
- Driving advances in simulation, scalable visualization, and data management
- Providing essential IT expertise across LLNL
- New simulation technologies and algorithms, such as in design optimization and decision support
- Computing beyond exascale: heterogeneous, neural, cloud/converged, and quantum
- Running one of the world’s largest control systems at NIF